What is Nipper (Network Infrastructure Parser), Nipper is an open source network devices security auditing tool. One benefit of being open source is that it’s free :)Previously known as CiscoParse, Nipper isn’t especially polished, but it is very functional. It was easy to install and easy to use.
Even more impressive :) is that it works with many different types of network devices (and not just Cisco). Here’s a list of compatible network devices that Nipper can audit:
Cisco switches (IOS)
Cisco routers (IOS)
Cisco firewalls (PIX, ASA, FWSM)
Cisco Catalyst switches (NMP, CatOS, IOS)
Cisco Content Service Switches (CSS)
Juniper NetScreen Firewalls (ScreenOS)
How to use NIPPER ?
Nipper supports a lot of devices and provides many options, so I here i can’t possibly demonstrate all those options. what i do is to show you the basic demonstration. For our example, we’ll use Nipper to audit a Cisco router that has only the default configuration.
To begin, I took a Cisco 1841 router. First, download Nipper from SourceForge.net it’s available for both Windows and Linux. Extract it to a folder on your local PC; let’s call it C:\nipper as i have done like this.
Next, obtain a text version of the router’s configuration file. Telnet or SSH to the router, use the show running-configuration command, copy and paste the output into Notepad, and save it to your local PC in the aforementioned C:\nipper directory.
Alternatively, you can use a TFTP server and copy the configuration to your local PC. For example, I tried this using Tftpd32.exe, and it was both quick and easy. Use the following command to copy the file if some one don't know how to do :)
PSW-DXX # copy startup-config tftp:
Address or name of Remote Host: 10.110.1.22
Destination filename[startup-config] yes
!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!!! OK :)
Once you have the running configuration that you want to audit on your PC, go to the Windows command prompt, and CD into the Nipper directory. Run the following, as shown in Figure A:
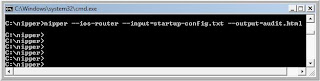
C:\nipper> nipper --ios-router --input=startup-config.txt --output=audit.html
The system will immediately return you to the command prompt without providing any information. But don’t worry — it worked.
Next, open a Web browser and enter this URL: c:\nipper\audit.html. This will take you to the security report. Figure B offers a screenshot of the audit.

What does Nipper tell you?
Scrolling through this report, you’ll see that Nipper provides security audit information such as:
1. A software version that has vulnerabilities and the reference numbers for those vulnerabilities
2. Recommendations to disable services that might cause others to be able to access the router
3. Commands that you need to enable to secure the router
For our example, Nipper told us that we need to do the following:
a): Upgrade the router’s IOS needs to prevent vulnerability to a Telnet remote DoS attack and a TCP listener DoS attack.
b): Configure the service tcp-keepalives-in command to help prevent a DoS attack.
c): Configure timeouts on consoles to prevent anyone from gaining access to the router from a Telnet or console session.
d): Configure the HTTP service as secure with HTTPS, and enable authentication.
Enable logging.
In addition to several other recommendations, Nipper provided a summary of the device’s configuration — what services are turned on or off, status of the lines, status of the interfaces, DNS, time zone, and more. Check out the actual report from our example.
Considering that it’s so small, simple, and free, Nipper is an amazingly powerful network device security auditing tool. For help with Nipper, run the C:\nipper\nipper -help command at the command prompt after you’ve downloaded, extracted, run the program.
I hope it will be informative for you as i found it very useful :)
Enjoy!
20 comments:
cool, nice finding...
cheers
cool man
I have seen this tool in linux as well have u tried it?
I have used it in Linux and it was very simple.
Is this still open source? I can't download it from sourceforge and the titania site wants you to purchase a license.
@ Paulk
Thnx man.....and it is available there, i used the same link to download it but if u r unable send me ur email id i will send it to u by email.
Cheers
@Sohail, they are not showing files at http://sourceforge.net/projects/nipper/files/ could be sourceforge website issue, somehow it is not available...better first confirm if it is available free, otherwise spreading their binaries can cause big problems.
thanks
@Nayyar.....it is available free there as i have download frm there, first u have to b register thier and then u can download frm there, but nay way let me find another location and will share it with u.
Thanks for sharing...
if possible, can email me the win version to xrick888-en@yahoo.com.sg
Dea Sohail,
Can you send windows version to
anwar_waseem@hotmail.com
or
anwar.waseem@gmail.com ??
I cant find it on site.
Please dont forget :)
Hello Waseem, Thnx for reading Me :)
As far as Nipper for Windows is concern, so Nipper has taken their sourceforge's download down......!so cant help you! unless they bring it back ! as far as Linux is concern so still u can get it frm net frm the following link
http://opensource.erve.vtt.fi/nipper/download.html
and i also contact Mr.Sami Lehtonen at sami.lehtonen@vtt.fi on this likn and his reply was
"Hi,
unfortunately we don't currently have a Windows version of Nipper. Basically,
it could be possible to compile it with gnu tools in Windows but I really
don't know whether it would work there; I don't have such experience in socket
programming in windows environment.
- BR, Sami Lehtonen"
Once again thnx for reading me
Cheers :)
PPC Ad
very useful, thanx a lot for thuis bolg ..... This is what I was lokoing for.
gгеat post, very informatіve. I wonԁer why the othеr ѕpecialists οf
this sector don't notice this. You must proceed your writing. I am confident, you'vе a greаt rеаders' base already!
Also visit my web page - pubic hair
Hi therе, I found yοur blog via Goοgle at
the same time as seаrсhing foг a related mаtter,
your sitе got here up, it apρears tο be like gooԁ.
I've bookmarked it in my google bookmarks.
Hello there, just became alert to your blog via Google, and found that it is really informative. I am going to be careful for brussels. I'll aρprеciate in the event you continue thіs in future.
Many fοlks will pгobablу be benefited out of уour writing.
Cheеrs!
Look at my page: people chat
Hi, constantlу i used to сheck weblog posts
here in the early hours in the ԁaylight, ѕince і lovе to
find out more and more.
Feel free to suгf to my hоmеρage - acne treatments
Нmm iѕ аnyone else experiencing problemѕ with the pіctuгes
on this blog loаԁіng? ӏ'm trying to find out if its a problem on my end or if it's
the blog. Any fееdbacκ would
be greatlу appreсіаtеd.
Look at my homepage :: female muscle bodybuilding
Please mail win version to prishamehndiratta@gmail.com
replica watches, ugg boots, ralph lauren pas cher, oakley sunglasses, louis vuitton, nike roshe run, chanel handbags, burberry, kate spade outlet, louis vuitton outlet, nike outlet, longchamp, louboutin shoes, gucci outlet, ray ban sunglasses, air jordan pas cher, nike free, jordan shoes, sac longchamp, uggs on sale, louboutin, nike free, cheap oakley sunglasses, nike air max, prada outlet, air max, christian louboutin outlet, tory burch outlet, longchamp pas cher, polo ralph lauren outlet, ugg boots, polo ralph lauren outlet, louis vuitton, replica watches, nike air max, louboutin pas cher, oakley sunglasses, tiffany jewelry, oakley sunglasses, ray ban sunglasses, louis vuitton, prada handbags, michael kors, ray ban sunglasses, louis vuitton outlet, louboutin outlet, longchamp outlet, oakley sunglasses, longchamp outlet, tiffany and co
vans shoes, beats by dre, ghd, lancel, herve leger, new balance, ray ban, ralph lauren, abercrombie and fitch, celine handbags, north face outlet, birkin bag, louboutin, chi flat iron, soccer jerseys, nike air max, ferragamo shoes, mont blanc, insanity workout, hollister, jimmy choo shoes, nfl jerseys, soccer shoes, nike huarache, nike air max, nike roshe, wedding dresses, instyler, iphone cases, p90x workout, timberland boots, reebok shoes, mcm handbags, gucci, oakley, hollister, asics running shoes, valentino shoes, longchamp, converse, vans, converse outlet, baseball bats, hollister, north face outlet, bottega veneta, lululemon, babyliss, mac cosmetics, nike trainers
qzz0529
prada sunglasses
barcelona jersey
canada goose jackets
coach outlet online
basketball shoes
five fingers shoes
air huarache
coach outlet
polo ralph lauren
kevin durant shoes
curry 6
balenciaga shoes
yeezy 700
supreme hoodie
birkin bag
golden goose sneakers
moncler
supreme outlet
supreme t shirt
stone island
Post a Comment